How to send Encrypted Emails in 2022

Using Pretty Good Privacy (PGP) to secure your emails from eavesdropping
When we send an email from top “free” e-mail providers such as Gmail, Yahoo or Hotmail, then our emails get logged on to their servers. They can read the content of your email and sell you products and/or sell your data to third parties for profits! NSA/GCHQ could be reading your emails and spy on you! However, you can make it a little difficult for them to do so by encrypting your emails communication.
If you want someone to send you a private or in technical terms an "encrypted" message, they need to have your “Public” key. The process is fairly simply once you know the basic things involved!
Pretty Good Privacy (PGP) is a way to help protect your email communications from being read by anyone except their intended recipients. And, to a lesser extent, it can save your emails from being read if the computer on which they are stored is stolen or broken into. It can also be used to prove that an email came from the intended person, instead of being a fake message sent by an imposter (it is otherwise very easy for email to be fabricated). Both of these are important defences if you’re being targeted for surveillance or misinformation.
The below process is for Macbooks but you can use similar process for windows without issues..
What do you need:
- A PC/Laptop/Computer (In this example, I am using a Macbook Pro)
- Download and Install gpgtools.
- Download and Install Thunderbird Email client. At the time of writing this article the current version is: 91.3.2
- Setup your email and generate public and private keys within Thunderbird client
What are Public and Private keys?
You can use gpgtools to create your public and private keys. As the name suggests, your public key is for you to distribute it to your friends, family, colleagues or anyone who wishes to contact you securely. One example could be that your lawyer wishes to send you some confidential files in the email, they can use your public key to encrypt the files and send you an encrypted email which only you can open and see.
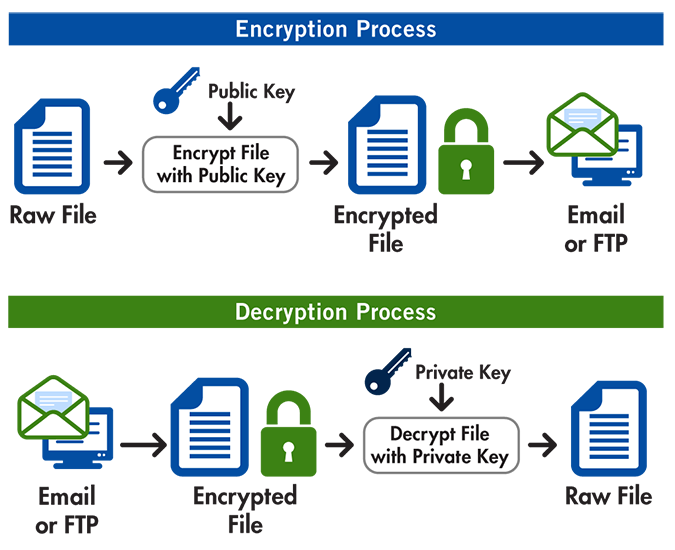
It uses the principle of pairs of public and private (or “secret”) encryption keys. To use OpenPGP, you must have a public and private key pair. Public keys are shared with anyone to whom you want to send encrypted messages, whereas private keys are never shared with anyone else. Private keys can also be used to decrypt messages encoded with the matching public key.
Thunderbird is an email client just like Apple mail. This makes it really easy to encrypt and decrypt emails. From Thunderbird version 78, It makes it super easy to generate public and private keys right from the thunderbird email client.
Now before I layout the steps, here is an overall picture of how PGP email encryption works:
Now open the thunderbird email client you just installed. It will ask you to setup your email account. You can setup any account like hotmail, gmail or yahoo. Once you set it up. You will see the mailbox. You can create a new key by:
Clicking on Tools > Account Settings
- Account Settings > select your email account > End-to-End Encryption > Add Key…
If you already have a personal OpenPGP key pair from another software, choose Import an existing PGP key.

If you don't have a key yet, choose Create a New OpenPGP key option as shown above.
- After importing or creating it, while still in account settings, select the key you want to actively use with your email account.
Note: It is important to make a backup of your key and store it in a secure location, separate from your regular computer. If you lose your private key, then you will not be able to decrypt any emails that were previously sent using its corresponding public key.
Now if you wish to send someone a secret/encrypted email with/without confidential documents, you will need their public key and vice versa.
Note: You should always compare the fingerprint of the key (Which is also listed in the thunderbird Account Settings. We use finger print because the original key is way too long to compare. So its like a shorthand for your key).
Here is what a decrypted email looks like when encrypted using the recipient's public key:

Notice the OpenPGP with the lock symbol in the screenshot. That's when you know that the email was encrypted and thunderbird decrypted it for you to see automatically. Effortless right?!?!
If you go into actual yahoo email account using a browser, you will see this:

As you can see that it cant be read via Yahoo because the private keys are stored on your local device! They can only see this 'Untitied' and 'encrypted.asc' files. No more snooping sucka!!!!
You must be thinking well what about the Sent folder on gmail (that's where I sent the encrypted email from). Well Let's have a look:

This proves that the encryption and decryption happens before the email leaves your computer! So they can’t see what’s been sent. It even concealed my subject line (Which can be revealing as well)
I also tested the same on Hotmail and they can’t see the contents + subject of my email either!
Now if you wish to read the email, you need to go back to thunderbird and open it there...This can be a hassle but security doesn't come cheap...!
Exporting your Keys out of Thunderbird:
Finally if you wish to export your keys out of thunderbird, do the following:
Tools > Account Settings > End-To-End Encryption > Look for your Key Hex number on the right handside and open the chevron > More Button > Export Public or Private key
So let's keep the conversation private :) Have a good one... ☝️
